Dismantle Entire Campaigns. Not Scattered IOCs.
Elite security teams don't chase indicators. They map complete adversary operations, predict infrastructure rotation, contain at operation level.
The Manual Correlation Trap Costs You Weeks
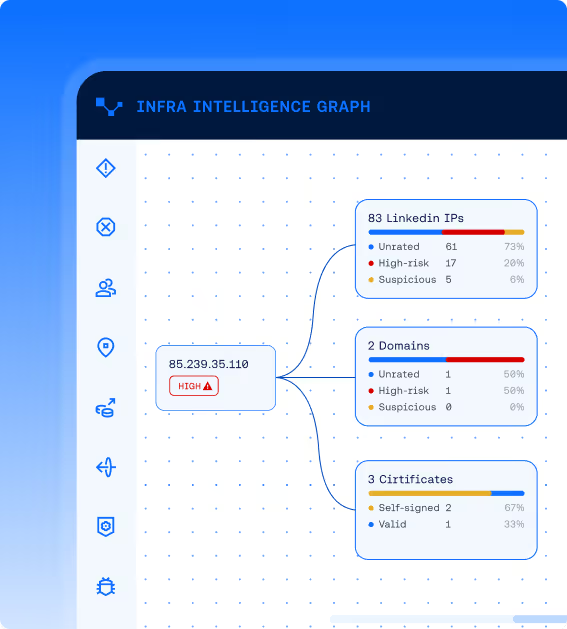
Analysts spend hours reconstructing campaigns across tools. By the time they connect dots, adversaries have rotated. Infrastructure Intelligence Graph maps complete adversary operations from scattered indicators. Pivot from any IP, domain, cert, ASN, or provider to reveal full campaign footprint instantly.
Unified correlation:
External infrastructure + internal patterns (SIEM, EDR, network) in minutes.
The Adversary Machine, Revealed in Real Time
Adversary Infrastructure Mapping
Live graph linking IPs ↔ domains ↔ certs ↔ ASNs ↔ services ↔ providers. Updates as infrastructure changes.
Infrastructure Pivoting
Navigate from single indicator to connected infrastructure across every dimension. One IP → 47 domains → 12 certs → full campaign. Instantly.
Campaign Clustering
Automatically connect related infrastructure into unified campaigns based on shared patterns and timing.
Relationship Analysis
Expose hidden links through infrastructure reuse, temporal behavior, TLS fingerprints, DNS patterns, hosting signals.
Evidence Trail
Every relationship backed by reason codes, confidence scores, time-stamped context. Defensible and audit-ready.
Internal Signal Correlation
Correlates findings with SIEM alerts, EDR detections, incident history. See which campaigns target YOUR environment vs. broader internet.
AI-Guided Investigation
Ask questions in natural language, generate pivots and hunt paths, produce briefings anchored to evidence.