Dark Infra Into Autonomous
Security Decisions
Security teams
are fighting blind
Analysts waste time triaging scanners, VPNs, CDNs, not real threats. AI-SOC agents hallucinate from lack of context. Adversaries build infrastructure at machine speed with an AI advantage, while you enforce in fragments.
Teams need unified,
pre-attack cyber risk intelligence that’s truly preventative
By fusing multiple intelligence sources into one predictive security layer, organizations can identify risky infra and stop attacks.
Pulse Sensors™
Proprietary telemetry from datacenter IPs and other data captures signals competitors miss
Your Internal Signals
SIEM, EDR, attack surface, network traffic, into one verified intelligence layer
See threats weeks before weaponization. Stop them at the origin. Eliminate the noise.

Pre-Attack
Intelligence
Pulse Sensors™ across worldwide datacenter IPs cut through anonymization, fingerprinting the entire global threat landscape. Detect infrastructure during build-out when others return "no data."
learn more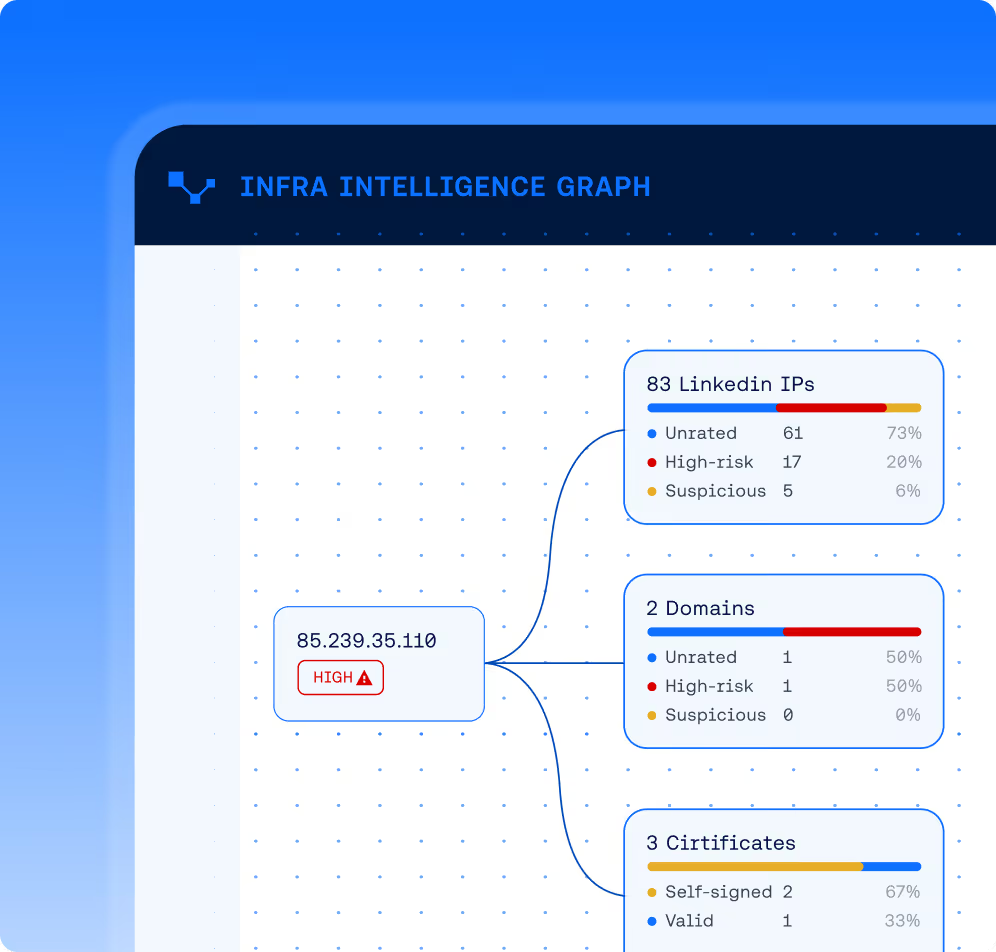
Infra Intelligence Graph + Explainable Risk Engine
Map complete campaigns from origin, not isolated black-box IOCs or scanner/VPN/CDN false positives. Explainable Risk Engine delivers reason codes, confidence levels, temporal context teams trust and automate.
Autonomous
Defense Enforcement
Decision Sync™ integrates directly with agents, propagates policies across SIEM, firewall, EDR, WAF, identity in seconds. Intelligence becomes action instantly.
learn moreWhy Teams Choose
VisionHeight
Evidence, not guesses
Explainable reason codes replace black-box scores with 90%+ indicator coverage.
Context, not noise
Origin Intelligence links IP, domain, certificate, and ASN, eliminating 70–80% of VPN/CDN false positives.
Early warning
Identify threats 2–8 weeks before weaponization, not after campaigns end.
Autonomous enforcement
Cut response times by 60%
Latest from
VisionHeight




