Evidence-backed automation. Not blind trust.
Elite security teams automating successfully don't hope tools are right. They know, every decision comes with evidence, confidence scores, reasoning they can defend to boards.
The Black-Box Automation Trap Kills Operations
Automation stalls when analysts don't trust scores they can't explain and leadership won't approve auto-blocking without proof. Explainable Risk Engine turns internet-scale signals into clear, defensible decisions with evidence, confidence, reasoning.
Multi-signal fusion: Dozens of data sources (external + internal) into explainable conclusions teams trust and defend.
Intelligence You Can Use at Machine Speed
Multi-Signal Fusion
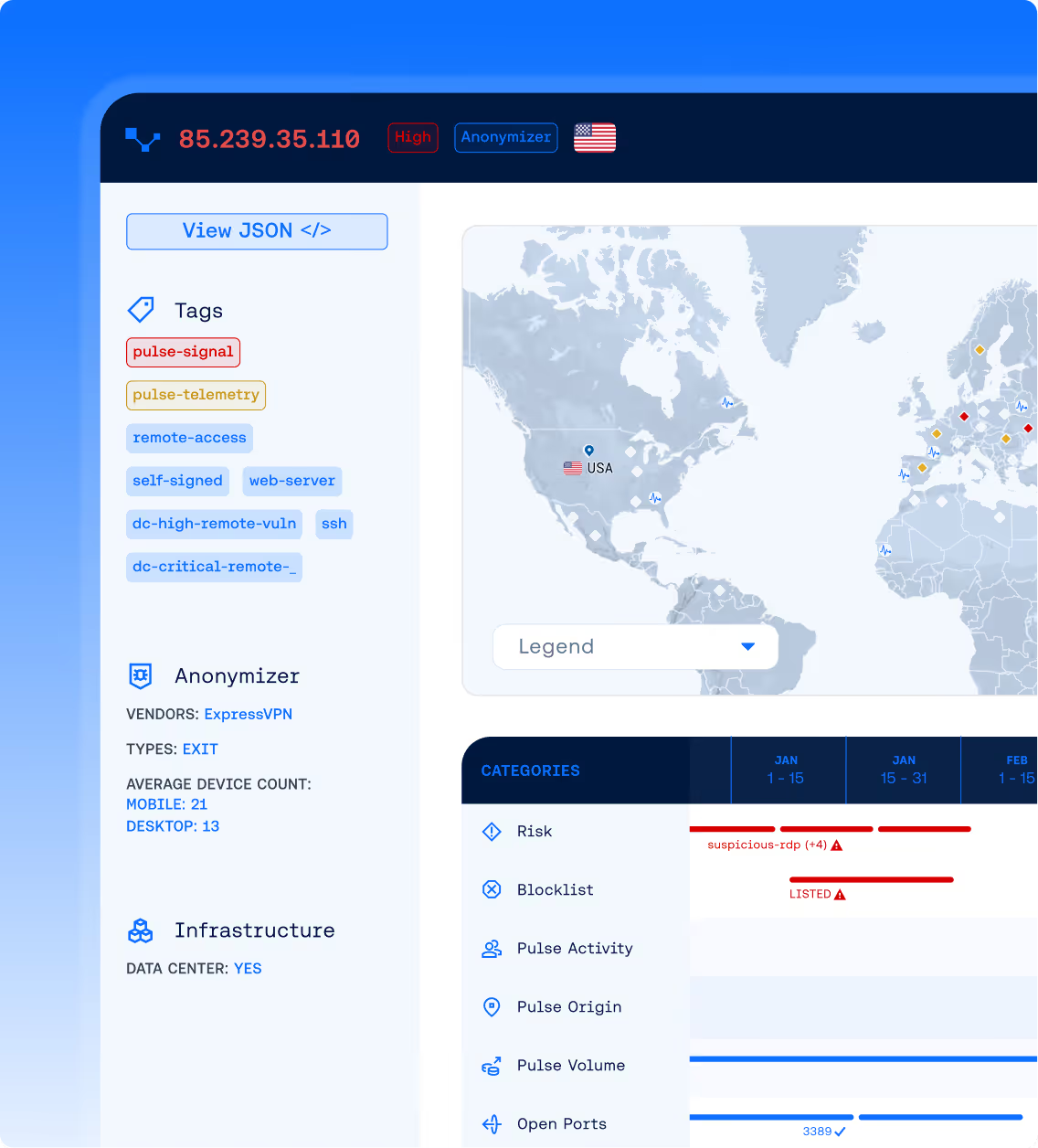
Combines telemetry, behavioral signals, DNS/WHOIS, certs, scanner context, honeypot signals, SIEM patterns, EDR detections. One explainable conclusion.
Internal Signal Enrichment
Correlates risk scores with attack surface data, vulnerability status, asset criticality, past incident patterns. Risk contextual to YOUR environment.
Real-Time Risk Scoring
Instant IP/domain risk with full reasoning, evidence, confidence, in milliseconds.
Predictive Threat Scoring
Forward-looking risk based on pre-weaponization signals and infrastructure patterns.
Internet Noise Filtering
High-precision classification: scanners, VPN/proxy, datacenter patterns, commercial services, threat infrastructure. Eliminate 70-80% false positives.
Context-Rich API
Enriched outputs built for automation: labels, services, exposure signals, provider ecosystems, behavioral patterns, internal correlation.
AI Decision Companion
Translates evidence into plain-language "why," suggests enforcement actions, helps generate hunt queries and playbooks.